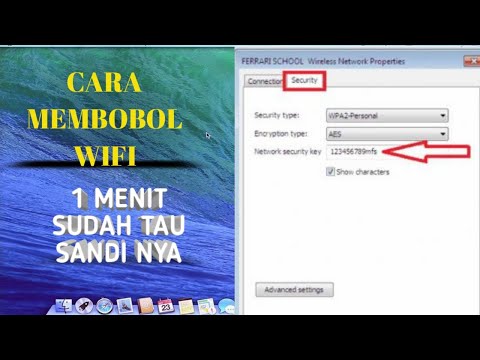
cara membobol wifi id di laptop

Title: Cara Membuka Semua Password WIFI
Channel: Mr. Anton
Cara Membuka Semua Password WIFI by Mr. Anton
Hack Any WiFi: Laptop WiFi Password Cracker Revealed!
Unlocking the Digital Fortress: A Look Beyond the WiFi Veil
Have you ever wondered about the invisible pathways that connect us? The ethereal tendrils of WiFi, weaving their magic through homes, cafes, and public spaces. It’s a ubiquitous technology, yet it often feels shrouded in mystery. We connect, we browse, but do we truly understand the security that protects our digital world?
The Allure of the Open Network: Why WiFi Security Matters
Think about it. Your laptop, a portal to the vast expanse of the internet. It holds your emails, your banking details, and perhaps even sensitive personal information. Securing your WiFi network is paramount; therefore, it's crucial. Now, consider the vulnerability of open networks. These can potentially expose your sensitive information. They are alluring, offering free access, however, they pose significant risks. It's like leaving the front door of your digital home unlocked.
Beyond Passive Observation: The Active Threat Landscape
The digital world isn’t static. It is dynamic and constantly evolving. The threat landscape is also in constant flux. So, understanding the active threats is important. "Password crackers" are a tool that exists. These are tools designed to crack WiFi passwords. Consequently, it’s essential to be aware of them. However, knowledge is power. Knowing about these tools helps us defend ourselves.
Fortifying Your Digital Perimeter: Practical Security Measures
You can take several measures to enhance your WiFi security. Let's explore some practical steps.
Strong Passwords are Key: Start with a strong password. Use a combination of uppercase and lowercase letters. Furthermore, incorporate numbers and symbols. Make it at least 12 characters long. Because of these measures, it becomes significantly harder to crack. Change your password often, too. This keeps your network secure.
Encryption: Your Digital Shield: Always use WPA2 or WPA3 encryption on your router. These are robust encryption protocols. They act as a shield for your data. They scramble your data, making it unreadable to unauthorized users.
Router Updates: Staying Ahead of the Curve: Keep your router's firmware updated. Manufacturers release updates to address security vulnerabilities. Install those updates promptly. As a result, you'll be protecting your network from known threats.
Hidden SSID: A Layer of Obscurity: Consider hiding your network's SSID (Service Set Identifier). Now, this won't make your network impenetrable. Yet, it does add an extra layer of obscurity. It makes it less visible to casual scanners.
Guest Networks: Isolating Your Guests: Create a guest network for visitors. This allows them to access the internet. However, it keeps them separated from your main network. Therefore, your sensitive data is protected, in case a guest is compromised.
Firewall Protection: Building a Digital Wall: Your router usually has a built-in firewall. Make sure it's enabled. A firewall acts as a barrier. It monitors incoming and outgoing network traffic. Therefore, it blocks suspicious activity.
The Ethical Implications: Navigating the Grey Areas
Let's address an important point: ethical considerations. Do not use any information learned here for illegal activities. Attempting to hack into someone else's WiFi network violates their privacy. It's also against federal and state laws. Instead, focus on securing your own digital environment.
Beyond the Basics: Advanced Security Considerations
For those seeking even greater security, there are advanced options.
MAC Address Filtering: Whitelisting Devices: Set up MAC address filtering. This allows only authorized devices to connect to your network. However, this can be time-consuming. Hence, it's a more involved security measure.
Regular Network Audits: Regularly audit your network. Examine your router's logs often. Look for any unusual activity. Moreover, you can use network monitoring tools to identify strange behavior.
The Future of WiFi Security: Staying Vigilant
The world of WiFi security continues to evolve. New threats emerge, and new technologies are developed. The key is to stay informed. Keep learning about the latest security practices. Be proactive in protecting your digital world. Remember, your online security is your personal responsibility.
Conclusion: Your Digital Fortress Depends on It
Securing your WiFi is more than just a technical exercise. It’s an essential act of responsibility. By implementing these measures, you fortify your digital fortress. You protect your privacy and sensitive information. Furthermore, you control your online experience. So, take charge today, and create a secure digital home for yourself and your family. The digital world awaits – safe and sound.
Laptop Wifi Nightmare? FIXED! (Easy Steps Inside)Hack Any WiFi: Laptop WiFi Password Cracker Revealed!
Alright, fellow internet explorers, let's dive right into something that's likely crossed everyone's mind at some point: how to crack a Wi-Fi password. Now, before you start picturing all the nefarious possibilities, let’s be clear: this isn't about malicious intent. It's about understanding the possibility and, more importantly, understanding the security measures in place to prevent such actions. Think of it as understanding the enemy to better defend your own digital castle. We're going to explore the fascinating world of Wi-Fi cracking using a laptop, focusing on the tools, the methods, and the crucial ethics that come with this knowledge.
1. The Allure of the Open Network: Why We Ask the Question
Let's be honest, the allure is real. You're at a café, your data plan is dwindling, and that tantalizing "Free Wi-Fi" sign is practically winking at you. Or maybe you're visiting a friend, and you'd rather not awkwardly fumble through a password reveal. The curiosity is natural, and the question, "Can I hack a Wi-Fi password from my laptop?" is a common one. Think of it like this: it's the same curiosity that leads you to try a new recipe, even though you know how to make your favorite dish. It's about exploration.
2. WiFi Security 101: The Basics You Need to Know Before Cracking
Before we even consider talking about the techniques, you need a basic understanding of Wi-Fi security protocols. Think of these protocols as the locks on the door to the internet. We have:
- WEP (Wired Equivalent Privacy): This is the grandpa of Wi-Fi security. It’s weak, easily cracked, and best avoided if possible. Think of it as a rusty padlock.
- WPA (Wi-Fi Protected Access): A significant improvement over WEP. It's more secure, but still, not impenetrable. Think of it as a combination lock.
- WPA2 (Wi-Fi Protected Access 2): The current standard and much more robust than its predecessors. It's like a modern, high-security deadbolt.
- WPA3 (Wi-Fi Protected Access 3): The newest and most secure. It uses even more advanced encryption methods. Think of it as a biometric fingerprint lock.
Knowing these basics is crucial. It's like knowing your opponent's fighting style before you step into the ring. The more secure the protocol, the harder it is (but not impossible) to crack.
3. The Laptop: Your Digital Swiss Army Knife for Wi-Fi Hacking
Your laptop is the key player here. It's the digital equivalent of your trusty Swiss Army Knife. It has the power, the processing capabilities, and, with the right software, the tools you need. The operating system (Windows, macOS, or Linux) and the built-in Wi-Fi adapter are your starting points. However, just like a Swiss Army Knife needs the right attachments; you'll need the right software, too.
4. Software Toolkit: The Arsenal of a Wi-Fi Cracker
Here’s where things get interesting. There are several software tools designed for Wi-Fi password cracking, some more effective than others. Let's look at a few:
- Aircrack-ng Suite (Linux): A popular choice for its versatility. It comes with a suite of tools for capturing packets, cracking WEP and WPA/WPA2 passwords, and injecting packets. Think of it as the entire toolkit in that digital Swiss Army Knife.
- Wireshark (Cross-Platform): Primarily a network protocol analyzer, but can be used to capture network traffic and potentially help in the cracking process (especially for analyzing vulnerabilities). It's like a powerful magnifying glass, helping you see what's happening under the hood.
- Cain & Abel (Windows): A powerful password recovery tool capable of sniffing network traffic, cracking various password types, and even testing Wi-Fi passwords. It's a more specialized knife, designed for a specific set of tasks.
- John the Ripper (Cross-Platform): This is a password cracking tool that can be used on captured password hashes. Think of it as a brute-force specialist.
It's important to note that using these tools ethically and legally is absolutely paramount.
5. Cracking Methods: A Peek Behind the Curtain
The methods used to crack Wi-Fi passwords vary depending on the security protocol used and the attacker's strategy. Here's a brief overview:
- Brute-Force Attack: Trying every possible password combination until the correct one is found. It's like trying every single key on a keyring until you find the one that fits. This is time-consuming, and only effective against weak passwords.
- Dictionary Attack: Using a list of common passwords to try against the network. It's like having a cheat sheet of common passwords.
- WPS (Wi-Fi Protected Setup) Attacks: Exploiting vulnerabilities in the WPS protocol, which allows you to attempt to retrieve the PIN for the access point.
- Packet Sniffing: Capturing the network traffic and attempting to crack the password from the captured information.
6. The Ethical Dilemma: Where Does Curiosity End, and Wrongdoing Begin?
Here's the crucial point: Wi-Fi cracking isn't just about the technical aspects. It’s about ethics. Accessing a network without permission is illegal and unethical, plain and simple. Think of it like trying to peek into someone’s house without their consent. There are severe consequences.
7. Legality Matters: Understanding the Laws in Your Area
The legal ramifications of hacking Wi-Fi passwords vary depending on your location. Some jurisdictions have more stringent laws than others. But generally, unauthorized access to a computer network is a criminal offense. Ignorance of the law is no excuse.
8. Defending Your Own Network: How to Secure Your Wi-Fi
The best defense is a good offense. By understanding how Wi-Fi passwords are cracked, you can better protect your own network. Here are some essential steps:
- Use WPA3 or WPA2: Always! WEP is a joke.
- Create a Strong Password: A long, complex password with a mix of uppercase and lowercase letters, numbers, and symbols. Think of it as fortifying your digital castle walls.
- Regularly Change Your Password: This limits the window of opportunity for attackers.
- Enable Two-Factor Authentication (2FA): If the router supports it.
- Update Your Router's Firmware: It's like patching the holes in your castle walls. Firmware updates often include security fixes.
- Hide Your SSID (Network Name): While not a strong security measure, it is a good first step.
- Limit Router Access: Set up a guest network that is separate from your own network.
9. Password Strength: From Weak to Unbreakable
A strong password is a must. Here's the difference:
- Weak: "password," "123456," your pet's name. Easily cracked.
- Strong: "Tr0ub4d0ur&D1v3r5e_$100n!." Complex, and difficult to crack.
10. The WPS Vulnerability: A Common Entry Point
WPS is meant to make connecting devices easier, but it can also create security vulnerabilities. It's like an unlocked door in your house. Many routers still have it enabled by default, which is a huge mistake. Disable WPS if possible!
11. Hardware Considerations: What About Specific Laptops?
The laptop's Wi-Fi adapter plays a role. Some older or cheaper adapters might lack the necessary features for packet injection, which is essential for many cracking techniques. Most modern laptops, however, are generally compatible.
12. Myth Busting: Common Misconceptions About Wi-Fi Hacking
Let’s dispel a few myths:
- Myth: "Hacking a Wi-Fi password is super easy." Reality: It requires technical knowledge and the right tools.
- Myth: "Anyone can do it." Reality: Not really. It requires some technical know-how and understanding of security protocols.
- Myth: "My router is impossible to crack." Reality: Everything can be hacked, given enough time and effort (and the right vulnerabilities).
13. The Future of Wi-Fi Security: What's Next?
Wi-Fi security is constantly evolving. We are seeing increased use of WPA3 and new standards, such as mesh networks equipped with enhanced security features, are emerging. It's a continuous game of cat and mouse, with security researchers constantly finding and patching vulnerabilities in routers and the software.
14. Learning and Growth: Expanding Your Knowledge
This is just the tip of the iceberg. To truly understand Wi-Fi security, delve into:
- Network Fundamentals: Learn about IP addresses, subnets, and how networks work.
- Cybersecurity Certifications: Consider studying for certifications such as CompTIA Security+ or Certified Ethical Hacker (CEH).
- Ethical Hacking Communities: Engage with ethical
Cara Hack Wifi viral wifihack Internet hacker

By Codeks 58 Cara Hack Wifi viral wifihack Internet hacker by Codeks 58

Title: Cara Bobol Wifi Voucher Pakai Laptop atau PC Terbaru 2024
Channel: HarunNamasela
Cara Bobol Wifi Voucher Pakai Laptop atau PC Terbaru 2024 by HarunNamasela
Working With Laptop
Here's your article:
Unveiling the Lost Art of Astronomical Clockwork: A Journey into the Grand Mechanism of Time
For centuries, humans have gazed skyward, captivated by the celestial ballet of sun, moon, and stars. This innate curiosity fueled a relentless pursuit: to understand the rhythms of the cosmos and, eventually, to capture them in exquisitely crafted machines. Among these marvels, the astronomical clock stands as a testament to human ingenuity, a breathtaking fusion of art, science, and engineering. This article will delve into the captivating world of astronomical clockwork, exploring its history, intricate mechanisms, and enduring legacy.
A Cosmic Symphony in Miniature: The Origins of Astronomical Clocks
The genesis of astronomical clocks can be traced back to the heart of medieval Europe, particularly the bustling city-states and thriving monasteries that served as crucibles of innovation. As early as the 14th century, these communities saw the emergence of the first rudimentary astronomical clocks. These weren't merely timekeepers; they were ambitious attempts to replicate the celestial sphere in mechanical form. These early clocks, often tower clocks, aimed to depict the positions of the sun, moon, and sometimes even the visible planets (Mercury, Venus, Mars, Jupiter, and Saturn) against the background of the constellations. The driving force behind this early innovation was the desire to provide accurate astronomical information for religious observances, astrological predictions, and civic functions. Monks and scholars, with their unique access to learning and resources, played a significant role in developing and refining these early devices.
The initial clocks were often powered by weight-driven mechanisms, relying on descending weights to turn complex gear trains. These gears, cut with impressive precision using methods like the verge escapement, were responsible for translating this power into the movements of the clock’s hands and astronomical dials. Early indicators were basic, but slowly they became enriched with more sophistication. By the 15th century, the clocks became more complex, with designs adding more features that displayed the time of day, the phases of the moon, and the position of the sun in the zodiac. The clock makers were in pursuit of creating a small model of the universe.
The Anatomy of a Celestial Machine: Exploring the Intricate Mechanisms
Dissecting an astronomical clock reveals a breathtaking array of interacting components, each meticulously crafted to replicate the subtle movements of celestial bodies. At its core lies the main timekeeping mechanism, often a pendulum or balance wheel regulated by an escapement that governs the rate at which the clock advances. This core is what keeps the time constant. This mechanism is then connected to a series of intricate gear trains. These gear trains are of varying sizes that ensure accuracy. These precisely cut gears work to drive the various astronomical displays.
One of the most fascinating of these displays is the celestial sphere, often a rotating dial or globe that depicts the stars and constellations. The celestial sphere usually rotates at a rate that corresponds to the apparent motion of the stars across the night sky. A prominent feature is often the zodiac dial, which shows the position of the sun in the zodiac throughout the year. This dial is connected to the solar hand, which completes one revolution per year, precisely tracking the sun’s annual journey against the backdrop of the constellations.
The phases of the moon are another common inclusion, often displayed by a rotating sphere with light and dark sides, or a disc that moves to display the moon’s phases. The lunar mechanism is linked to the main timekeeping and is precisely geared to mimic the moon's 29.5-day lunar cycle. Other advanced clocks include depictions of planetary motion. These complexities require a greater number of gears and meticulous planning to simulate the celestial orbits. A planetary display will often incorporate small representations of the planets that move in relation to the sun, showing their position in the zodiac.
Masterpieces of Craftsmanship: Notable Astronomical Clocks Through History
Throughout history, certain astronomical clocks have achieved iconic status, becoming symbols of human artistry and scientific achievement. The Prague Astronomical Clock, also known as the Orloj, is perhaps the most famous. Installed in 1410 on the Old Town Hall in Prague, it represents a stunning display of engineering, horology, and aesthetic expression. The clock includes an astrolabe dial, which shows the position of the sun and moon along with other astronomical details. Every hour, the clock’s mechanical figures enact a short performance, that includes the movement of the apostles. The Orloj has been repaired and restored over the centuries, and its enduring popularity lies in its elaborate mechanics. The Prague Astronomical Clock is an exquisite example of the art and science of astronomical clockmaking.
Another masterpiece is the Strasbourg Astronomical Clock, built in the 16th century. The clock features displays of the planets, the days of the weeks, and the time of day. It is also adorned with elaborate figures that move on the hour, including those of Christ and his Apostles. The clock’s architectural context adds to its splendor, with its location in a cathedral, which highlights its connections to religious observance.
The astronomical clock at Wells Cathedral in England, dating from the 14th century, is another example of a preserved historical astronomical clock. This clock displays the sun, moon, and stars and features a dial that predicts the positions of the planets. This clock is one of the oldest of its kind in the world. The clock at Wells Cathedral is a testament to the skills of medieval clockmakers.
The Enduring Legacy: Astronomical Clocks in the Modern World
Though modern technology has rendered the astronomical clock functionally obsolete as a means of telling time, the enduring fascination with these devices persists. Today, these marvels of engineering are treasured as historical and cultural artifacts. They are appreciated not only as functional timekeeping devices but also as sophisticated works of art. Museums around the world showcase these clocks, allowing visitors to marvel at the intricacy of the mechanisms and to contemplate the historical context in which they were created.
The principles of astronomical clockwork have also had an impact on modern technology. Precision gear cutting, mechanical movements, and an understanding of celestial mechanics have all found applications in other fields. From the early days of the mechanical computer to precision measuring devices, the principles developed by astronomical clockmakers have found practical applications as well.
Moreover, the aesthetic of astronomical clocks has influenced modern design and architecture. The rich detailing of the dials, the precision of the hands, and the incorporation of planetary symbols continue to inspire artists and designers. Astronomical clocks are not relics of the past, but a source of inspiration for modern creativity.
Conclusion: Echoes of the Cosmos
The astronomical clock is more than just a timepiece; it is a microcosm of the universe, an expression of mankind's quest to understand the heavens. From the earliest tower clocks to the ornate masterpieces of the Renaissance, these intricate machines capture the celestial dance. By taking a deep dive into the world of the astronomical clock, we can gain a deeper appreciation for the historical, cultural, and artistic significance of these marvels of engineering. They stand as an enduring testament to human ingenuity, a reminder of our ceaseless curiosity about the cosmos.